Overview
Routing Protocol Authentication
- Main tool for securing routing information
- route injection/deletion/modification etc.
- Auth Method
- Clear text
- Hash-based
- IPsec
- clear text auth is not security tool
Key chain
- configuration component used to store authentication key
- allow for key rollover
- accept lifetime control how long key is used for verification incoming updates
- send lifetime control what key is used to authenticate outgoing updates
- Lifetime overlap is recommended to avoid authenticate failures.
- allow for key rollover
Configuration
key chain name (localy significat) key id (must same)
EIGRP
there are 2 method for securing EIGRP
1. Authentication
- EIGRP support md5 and SHA-256 (named mode)
- Classic mode in interface mode.
- key chain eigrp key 1 key-string myeigrp # attach to interface eigrp ip authentication mode eigrp 1 md5 ip authentication key-chain eigrp 1 eigrp # verification show ip eigrp interfaces detail ethernet 0/0
- Named mode in keychain configuration.
2. Prefix Limit
- protect local system resources against EIGRP miss config
- set a threshold for a maximum number of accepted rules
- neighbor based
- all of the neighbor
- Redistribution routes.
- Modes of operations
- default: remove all routes from offending peer and suspend it (penalty timer)
- warning: generate syslog without removing rotes/routers
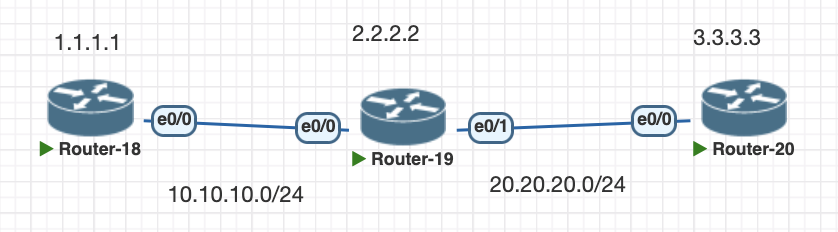
Topology
Testing Scenario
- configure classic authentication between R1 and R2
- configure authentication with sha-256 between R2 and R3
- Limit prefix route in EIGRP on R2
Configuration
- configure classic authentication between R1 and R2
# create key chain on both routers
key chain eigrp
key 1
key-string myeigrp
router eigrp 1
network 1.1.1.1 0.0.0.0
network 10.10.10.0 0.0.0.255
interface Ethernet0/0
ip authentication mode eigrp 1 md5
ip authentication key-chain eigrp 1 eigrp
duplex auto
# configure on both router with same passwordfor verification we can use this command
show ip eigrp interfaces detail ethernet 0/0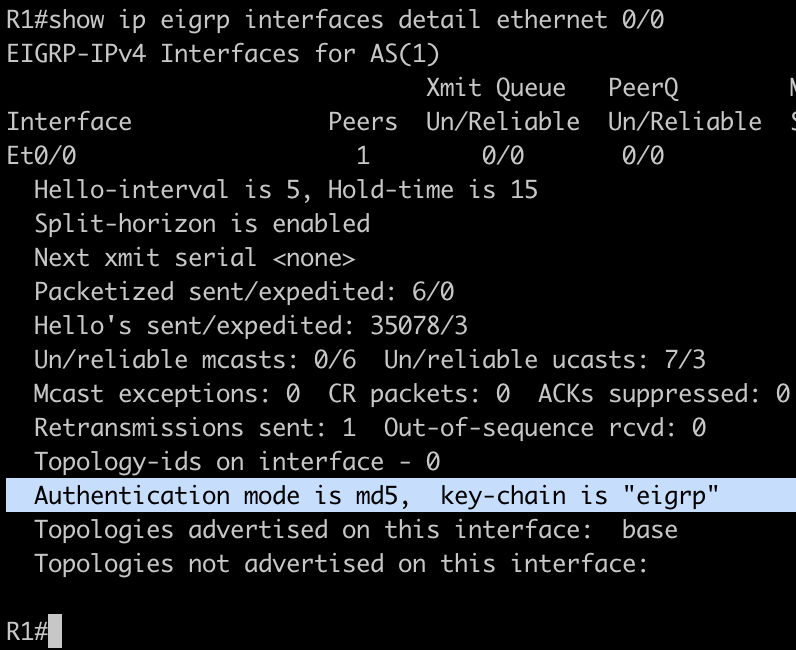
2. configure authentication with sha-256 between R2 and R3
# configure the authentication in EIGRP name mode address family
router eigrp R23
!
address-family ipv4 unicast autonomous-system 2
!
af-interface eth 0/0
authentication mode hmac-sha-256 myeigrp
exit-af-interface
!
topology base
exit-af-topology
network 20.20.20.0 0.0.0.255
Verification:
show ip eigrp interface detail eth 0/1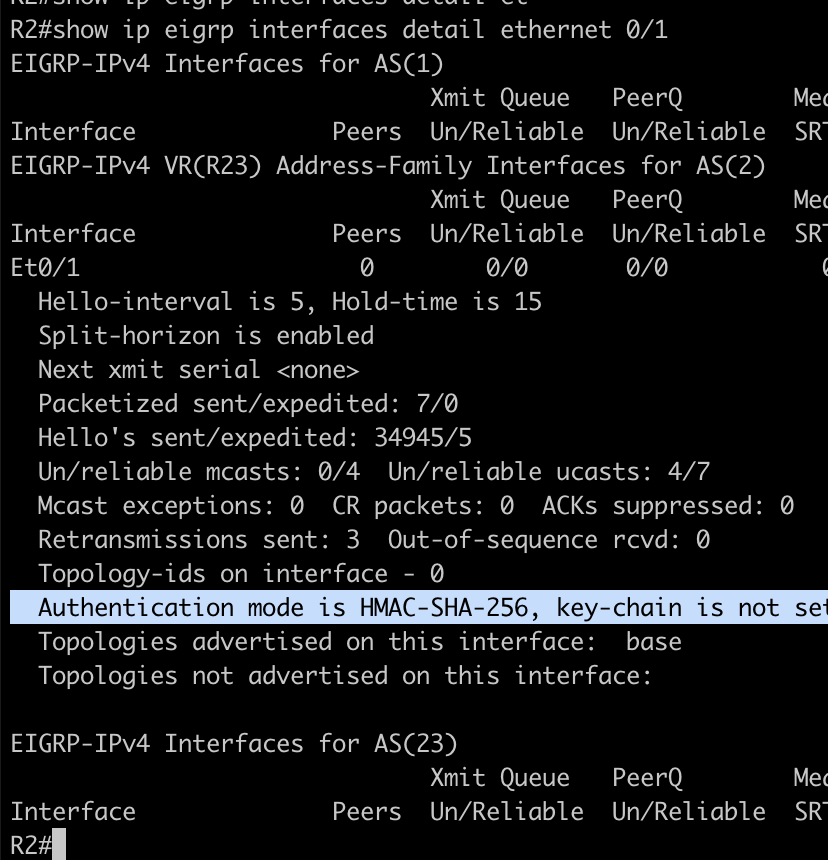
3. Limit prefix route in EIGRP on R2
# set maximum limit for router R2 in eigrp process
router eigrp R23
!
address-family ipv4 unicast autonomous-system 2
!
af-interface default
authentication mode hmac-sha-256 myeigrp
exit-af-interface
!
topology base
exit-af-topology
network 20.20.20.0 0.0.0.255
maximum-prefix 2 ## this limit prefix
exit-address-familyVerifications, when router or neighbor reach limit prefix it will hold the neighbor for negotiations.
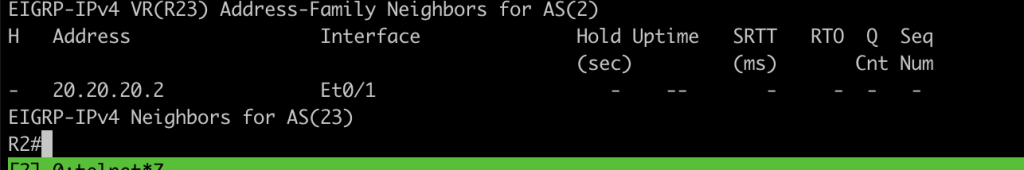
the timer is not shown means the negotiation is pending state.
Conclusions
- We can use multiple authentication type based end hash md5 or sha depend on the requirements.
- To prevent route injection from redistribution or BGP we can use prefix limit
If you found this useful, subscribe to newsletter