Overview
Authentication
- BGP vulnerabilty can be found in 4272
- BGP is different from other IGP because its not run in own protocol, its run using TCP 179
- BGP and mBGP can be authenticated with MD5 or IPsec
- the hash is store inside TCP option 19
- any packet modification by NAT or ASA randomization
- configuration
- neighbor [address] password
GTSM (Generalized TTL Security Mechanism)
- RFC 5082
- This will prevent Spoofing neighbor
- Method of validating IP packet based on their TTL/Hop Limit value
- very effective against CPU utilization attacks.
- packet with non-confirming TTL/Hop limit will discarded
- Especially useful for BGP
- work only for eBGP peer
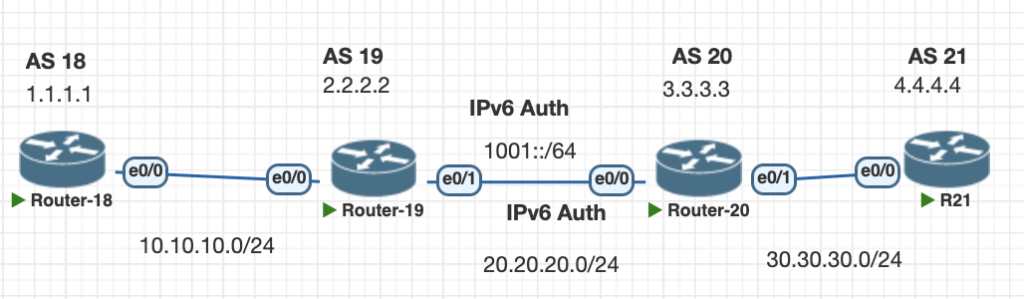
Topology
Testing Scenarios
- Configure authentication BGP between R18 and R19
- Configure authentication BGP ipv6 between R19 and R20
- Configure security GTSM for Router R19 facing neighbor R21
Configurations
1. Configure Authentication BGP R18 and R19
# R18
router bgp 18
neighbor 10.10.10.2 remote-as 19
neighbor 10.10.10.2 password mysecret
#R19
router bgp 19
neighbor 10.10.10.1 remote-as 18
neighbor 10.10.10.1 password mysecretverifications show the neighbor status, there is no detail authentication is being used in IOS
show ip bgp sum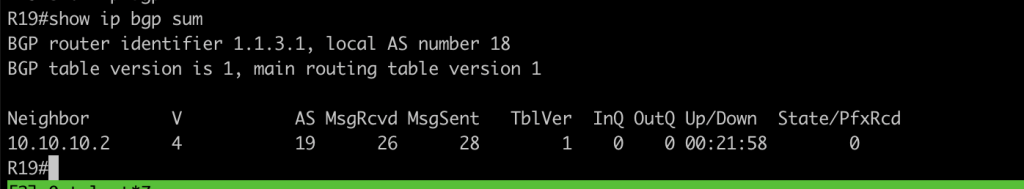
2. Configure Authentication BGP IPv6 between R19 and R20
# R19
router bgp 19
neighbor 1001::2 remote-as 20
neighbor 1001::2 password ciscopassword
address-family ipv6
neighbor 1001::2 activate
# R20
router bgp 20
neighbor 1001::1 remote-as 19
neighbor 1001::1 password ciscopassword
!
address-family ipv6
neighbor 1001::1 activateverification we can check the neighbor status
show bgp ipv6 unicas sum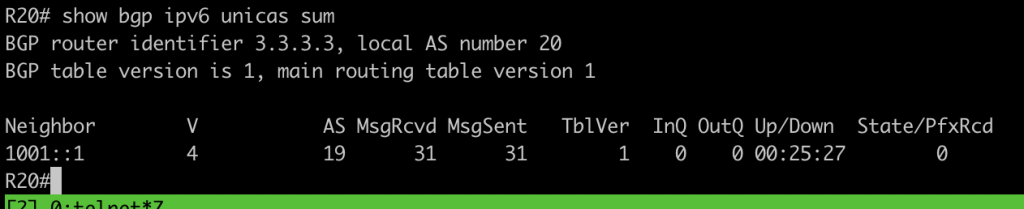
3. Configure security GTSM for Router R19 facing neighbor R21
#R19
router bgp 19
neighbor 30.30.30.2 remote-as 21
neighbor 30.30.30.2 ttl-security hops 2
#R21
router bgp 21
neighbor 20.20.20.1 remote-as 19
neighbor 20.20.20.1 ebgp-multihop 255verification we can check the neighbor status and detail for the neighbor
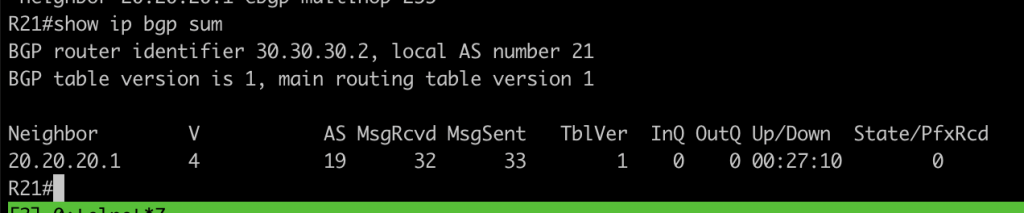
show ip bgp neighbors 30.30.30.2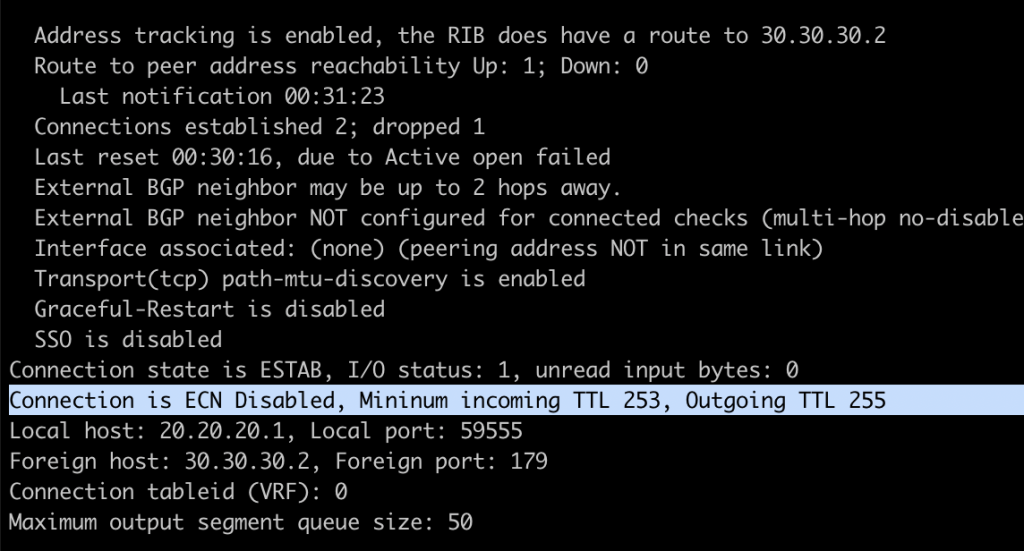
Conclusions
- With authentication we hardening neighbor relationship.
- In production network we can configure both authentication and GTSM
If you found this useful, subscribe to newsletter