Overview
uRPF (unicast reverse path forwarding)
- RFC 3704 for unicast Ipv4
- ingress filtering is only for single homing, but for multi homing is not scalable
- CEF must be enabled
What
- perform some validation source ip address of packet
- if the source is not valid will be dropped
Which packet
- multicast packet enabled by default
- unicast disable by default
What is the purpose
- Multicast: loop prevention and multicast tree building
- Unicast: prevent IP spoofing
Mode uRPF unicast based 3704
- strict RPF , feasible path, loose RPF
- IoS support strict and loose RPF based on FIB entry.
Strict uRPF overview
- packet is accepted only if it was received on the RPF interface
- RPF interface mean: identifies the egress interface the router would use to route for the source ip packet.
Considerations
- not compatible with asymetric networks.
- ECMP route and UCMP (Eigrp) is compatible
- optionally enable RPF on default route.
Loose uRPF overview
- packet is accepted as long as the router has a route for the source IP packet
- traffic with source null0 will be dropped
- compatible with asymetric routing
- Route usable by uRPF this mode is :
- any route except default route
- optionally we can add default route.
Advance uRPF
- we can add acl to uRPF for advance feature.
- if the packet drop by uRFP the router will check ACL if the ip packet is accepted or not.
- ACL with permit permission:
- if the packet is drop by urpf and want allow we can just add acl to the source.
- This use for whitelist ip.
- ACL with deny permission:
- if the packet is dropped and want to log/know which source ip is spoofed.
- this used to identify which source are being spoofed by using log option into ACE
Troubleshooting uRPF
- ensure uRFP is configured on inbound interface (its inbound feature)
- ensure proper mode (strict or loose)
- for loose mode verify the existence of null0 route for the source.
- verify FIB decision for that source
- verify acl is being configured.
Topology
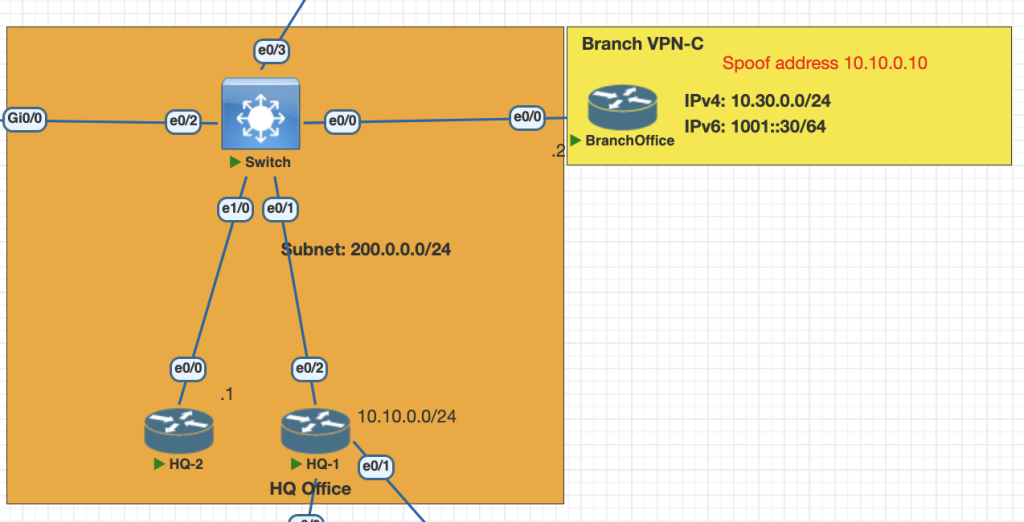
Testing Scenarios
- Branch C will be act as attacker and spoofed IP address 10.10.0.10, the victim is HQ-1 Network which is has validate network 10.10.0.0/24.
- Configure strict uRPF HQ-1 to prevent DoS/DDOS spoofed ip address from Branch C.
- Branch B will be act as attackeer and spoofed IP address 10.20.0.10, the victim is HQ-2 network whic is has validate netwokrk 10.20.0.0/24
- Configure loose uRFP HQ 2 to prevent spoofed DOS/DDOS ip address from branch B
Configurations Strict uRPF
- create fake spoofed ip address on Branch C.
# branch C
int lo1
ip address 10.10.0.10 255.255.255.2552. verify the HQ-1 has valid route for 10.10.0.0/24 network in CEF table
show ip cef 10.10.0.10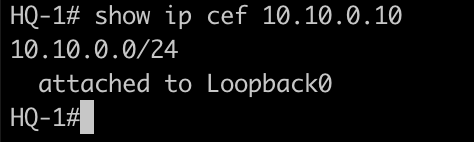
3. Configure uRPF on inbound interface HQ-1
interface Ethernet0/2
ip verify unicast source reachable-via rx
###if you want also check with default route RPF check (Optional)
int eth 0/2
ip verify unicast source reachable-via rx allow-default Verifications strict uRPF
- Enable debug ip icmp on both branch C and HQ-1
debug ip icmp2. Test ping connection from Branch C to HQ 1 using spoofed ip address
ping 10.10.0.1 source lo1 repeat 3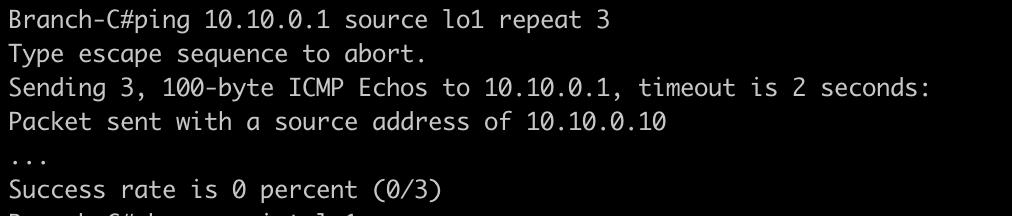
3. check the interface eth 0/2 and cef interface is droping the spoofed ip address
show ip int eth 0/2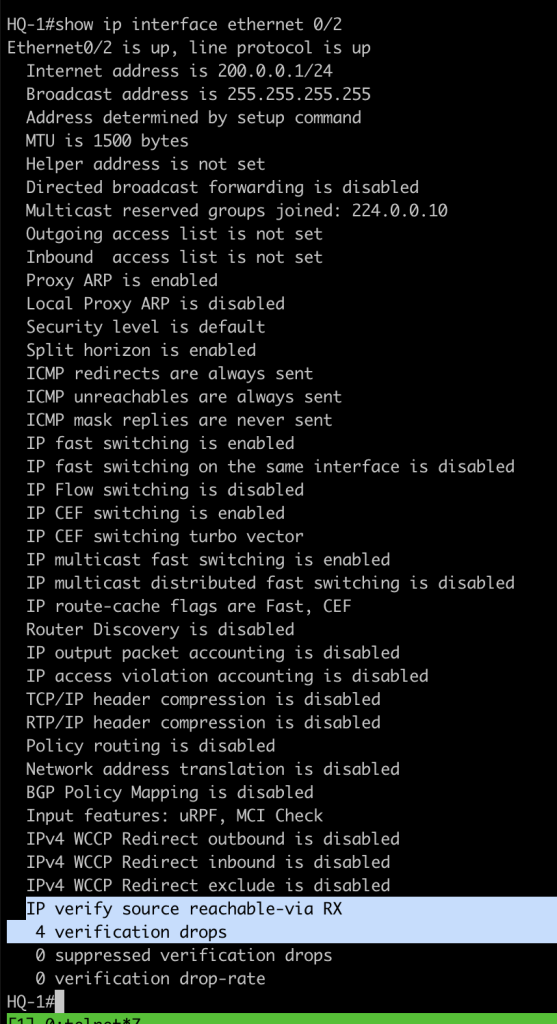
show cef interface ethernet 0/2 internal | i verify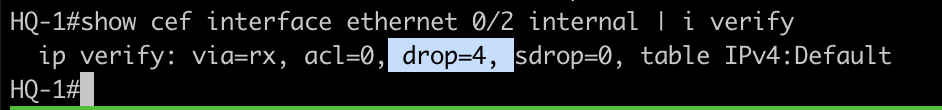
Configuration Loose uRPF
- configure fake ip address on branch B
int lo 1
ip address 10.40.0.20 255.255.255.2552. enable debug icmp on HQ-2 to verify packet icmp is received
debug ip icmp3. configure loose uRPF in HQ-2
int eth 0/0
ip verify unicast source reachable-via any
# if you want to add checking with default route add this.
int eth 0/0
ip verify unicast source reachable-via any allow-default Verification Loose uRPF
- testing ping from attacker branch B
ping 10.40.0.1 source lo1 repeat 12. check the interface statistic and cef
show cef interface eth 0/0 internal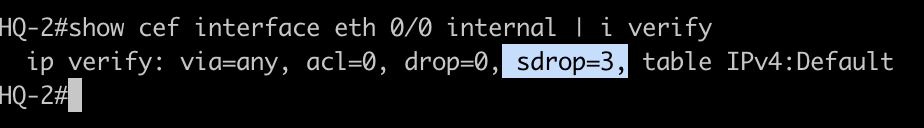
sdrop means: the packet is still forwarded even the source ip attacker is not same with arrival interface.
Conclusions
- use Strict uRPF for use case Access/edge (ISP, campus) bacause the traffic moslty is symetric.
- use loose uRPF for use case Core, DC, internet edge because the traffic is asymetric.