What RTBH
- its a packet filtering technique that allow dropping undesirable traffic at the edge of your network.
- its used to stop dos and DDOS attacks
How it work
- Relies on remote iBGP update in order to black hole traffic
- work for both IPv4 and IPv6
- RTBH can block based on
- Destination ip address packet
- source ip address packet
How does Destination Based RTBH work?
- all edge iBGP router have a null 0 route for prefix (RFC 6666 defines the discard prefix for IPv6).
- when a destination is under attack, a BGP speaker called trigger router, will trigger an iBGP update.
- This update contain a route for the attacked destination with next hop of prefix which is null0 routed.
What is the outcome?
- all traffic towards the destination is dropped inbound at the edge of your network.
Implementation steps
- Have iBGP configured
- configure the null 0 route on your edge iBGP routers
- when under attack. trigger iBGP update for the destination of the attack.
How does Source Based RTBH work?
- all edge iBGP router have a null 0 route for prefix (RFC 6666 defines the discard prefix for IPv6).
- All iBGP edge router have uRPF in loose mode configured.
- when a destination is under attack, a BGP speaker called trigger router, will trigger an iBGP update.
- This update contain a route for the attacked destination with next hop of prefix which is null0 routed.
What is the outcome?
- all traffic from source of attacked is dropped inbound at the edge of your network.
RTBH comparison source and destination
- Destination based RTBH
- drop all incoming traffic for the destination of the network (legit and malicious)
- good in DDOS when there are too many sources
- Sources based RTBH
- drop all incoming traffic from source of the attack, legit traffic still work
- Good in DOS and DDOS with not too many source
Topology
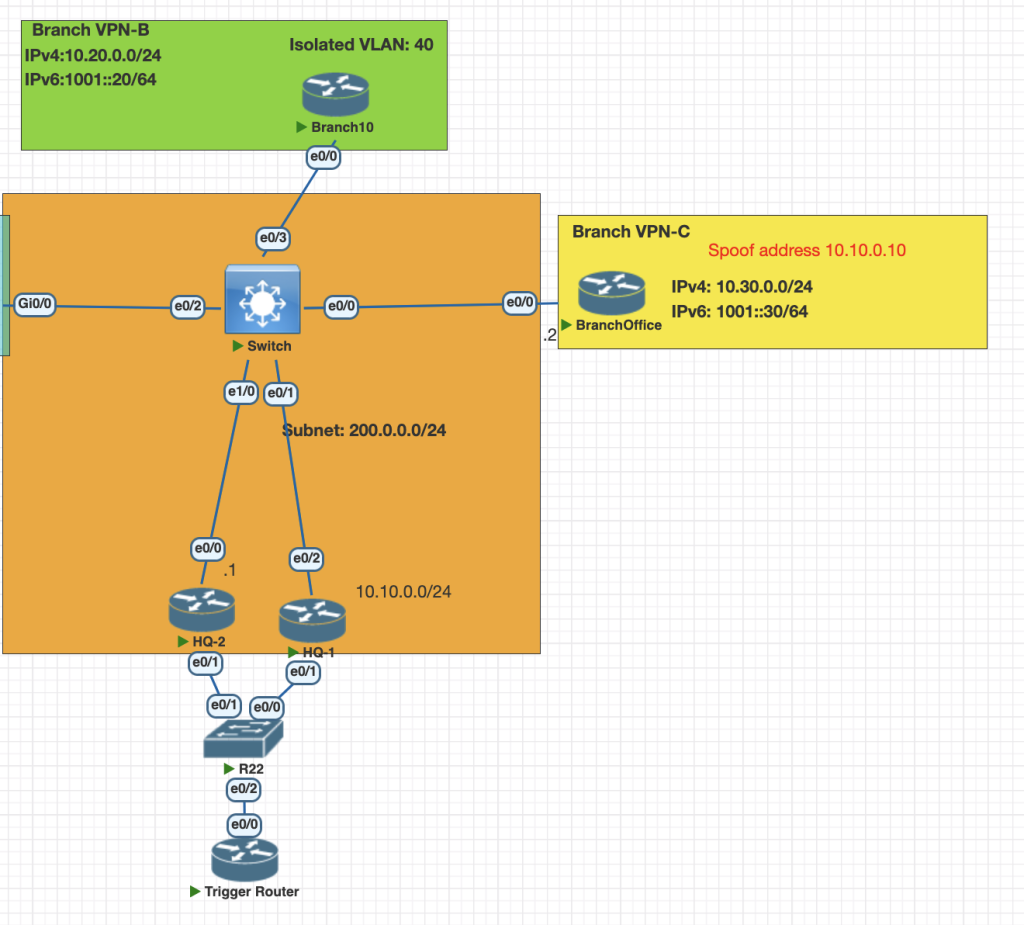
Testing Scenario
- The victom for this scenario os IP 192.168.100.10
- The attacker for this is Branch B with ip address 200.0.0.2.
- Configure iBGP between HQ1 , HQ2 and Trigger router.
- Configure route map on trigger router to trigger route update when attack is occur.
- Create 2 scneario with Destination RTBH and Source RTBH.
- Confogure HQ1 and HQ2 uRPF loose mode for source RTBH.
Configuration
- configure iBGP for each internal router HQ1, HQ2 and trigger router
# HQ1
router bgp 100
bgp log-neighbor-changes
redistribute static
neighbor 10.10.0.3 remote-as 100
neighbor 200.0.0.4 remote-as 100
neighbor 200.0.0.4 update-source Ethernet0/z2
# HQ2
router bgp 100
bgp log-neighbor-changes
redistribute static
neighbor 10.10.0.3 remote-as 100
neighbor 200.0.0.1 remote-as 100
neighbor 200.0.0.1 update-source Ethernet0/0
# Trigger Router
router bgp 100
bgp log-neighbor-changes
redistribute connected
neighbor 10.10.0.1 remote-as 100
neighbor 10.10.0.2 remote-as 1002. Configure static route for black hole prefix
# HQ 1 and HQ 2
ip route 169.254.0.0 255.255.0.0 Null03. configure route-map on router trigger to match if an attack occurs
route-map RTBH-Trigger permit 10
match tag 90
set local-preference 900
set ip next-hop 169.254.1.1
router bgp 100
redistribute static route-map RTBH-TriggerVerification
- Destination RTBH: configure static routing on trigger router to update victim ip address
ip route 192.168.100.2 255.255.255.255 Null0 tag 902. Source RTBH: configure static routing on trigger router to update attacker ip address
# first configure uRPF loose mode in edge router
int eth 0/2
ip verify unicast source reachable-via any
# Trigger Router
# add static route attacker ip address branch B
ip route 200.0.0.2 255.255.255.255 Null0 tag 903. check the route for 200.0.0.2 is black holed in edge router
show ip route 200.0.0.2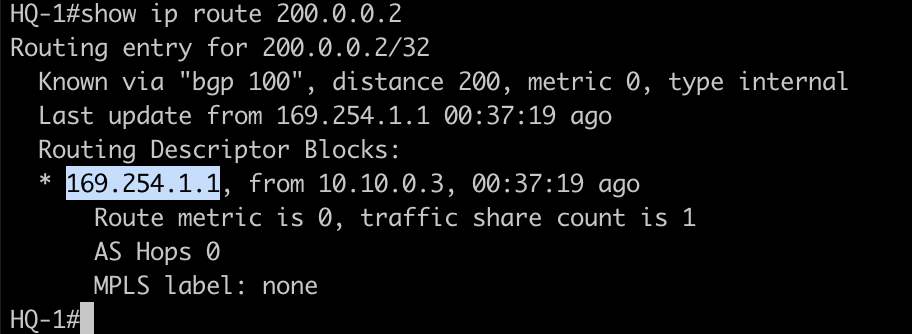
This next hop is is belong to black hole prefix.
4. Testing connection from Branch B and Branch
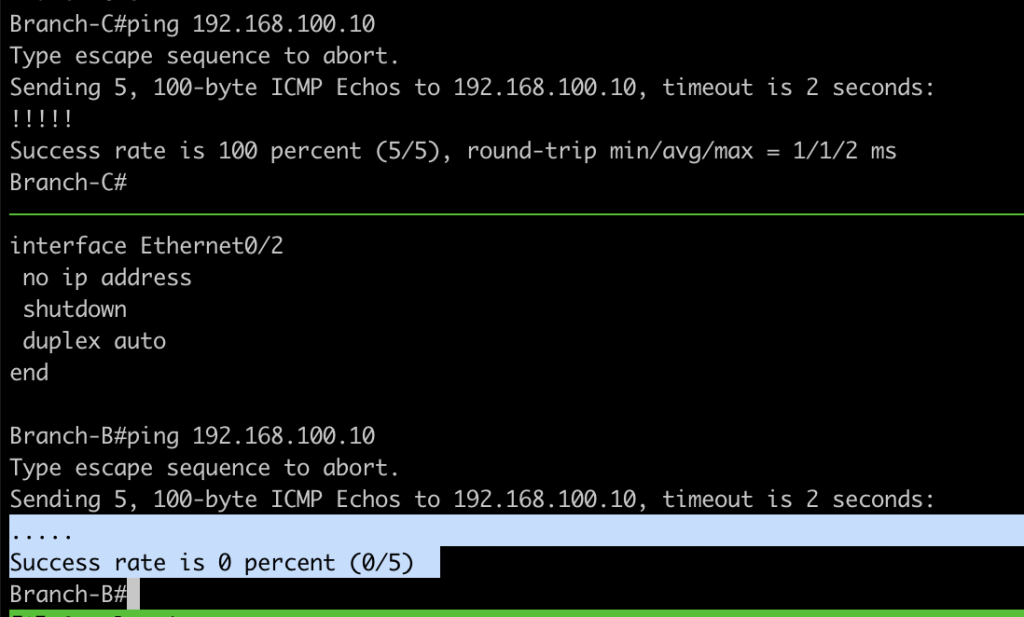
Traffic From Branch is blocked by edge with uRPF and iBGP
# edge HQ1
show ip int eth 0/2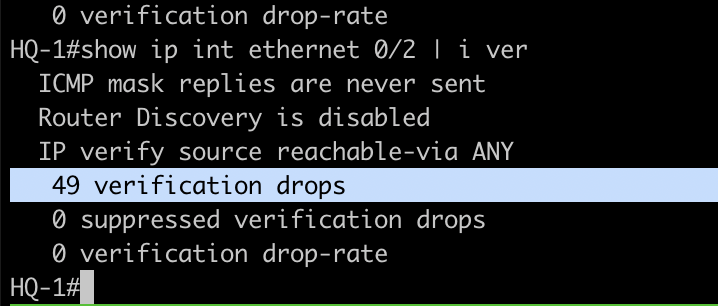
Reference
Ciscocisco.com/c/dam/en_us/about/security/intelligence/blackhole.pdf