Overview
- GETVPN (Group encrypted transport vpn) is a sclabable IPsec-based encryption tech.
- In traditional IPsec Tech if we are using static tunnel or DMVPN we have many connection to each site. for example if we have 6 site.
- formula: m(m-1)/2
- m=site
- 4(4-3)/2 = 6 connection total, to create full mesh connections.
- if we total to the control plane session
- 6 connections for IKE SA
- 2 x6 connection IPSec. (1 for Control Plane and 1 for Data plane)
- Commonly used to protect intra-wan Traffic
- does not work in over internet (in most cases)
Benefit GETVPN
- easy to deploy on an existing infrastructure
- no need for an overlay network
- resource efficient for each devices in the network. because only maintain 1 IKE SA
GETVPN devices
- key Server
- source of control plane informations
- create/stores ipsec SA & keys
- Responsible for rekeying
- normally not used in Data Plane
- Group Member
- Part of Data Plane
- Encrypt/Decrypt the traffic using shared SA.
GETVPN Control Plane
- Group domain of Interpretation (GDOI) – RFC 6407
- SA information is pulled during registration (GMs-KS)
- GM provide ID of group to join
- KS replies with policy.
- if GMs accept the policy, KS return SA
- and a set cryptographic key.
- Traffic encryption key
- key encryption key
- RSA public key
- GDOI use ISAKMAP or IKEv2 to protect the registrations
- work over UDP 848
- Rekeying
- Process of refreshment the group SA with new keys.
- Keys are pushed (KS → GM)
- unicast
- multicast ( default method require multicast routing protocol)
GETVPN Data Plane
- GETVPN requires a working data plane
- address preservations (reusing the original IP information for tunneling AH and ESP)
- no need additional IP address or routing.
- Not a Problem in a single site
- Inter-site communication require full connectivity.
- internet itself is usually not an options
- use Private WAN.
Topology
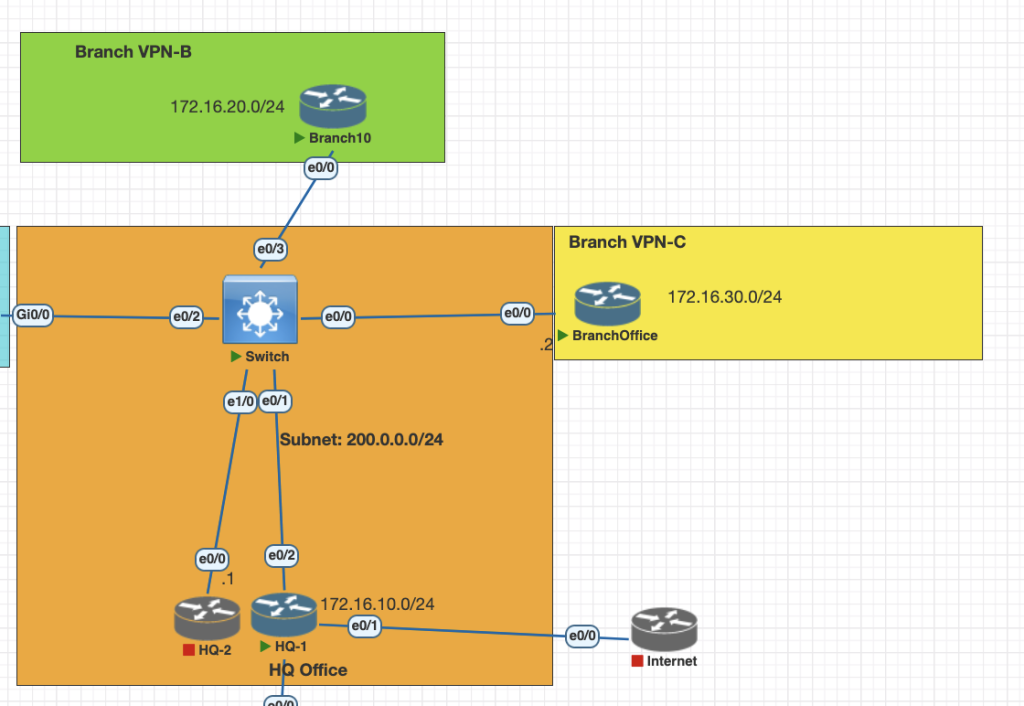
Testing Scenarios
- Configure HQ1 as KS for GETVPN in the network.
- Configure Branch VPN B and C as GM for GETVPN
- Make sure all internal connectivity 10.0.0.0/8 is encrypted via IPsec for communication between site
- Configure rekey using unicast.
Configuration Steps
Configuration HQ as KS
- Generate RSA key for rekeying
crypto key generate rsa label GETVPN modulus 20482. define ipsec profile and access list for interest traffic for IPsec.
crypto ipsec transform-set SET1 esp-aes esp-md5-hmac
mode tunnel
crypto ipsec profile IPPOF1
set transform-set SET1
access-list 120 permit ip 10.0.0.0 0.255.255.255 10.0.0.0 0.255.255.2553. create rsa for rekey method
crypto key generate rsa label GETKEY modulus 20484. configure GETVPN GDOI
crypto gdoi group GET
identity number 10 # must identical between
server local
rekey authentication mypubkey rsa GETKEY
rekey transport unicast
sa ipsec 1
profile IPPOF1
match address ipv4 120
replay counter window-size 64
no tag
address ipv4 200.0.0.15. Create IKEV1 profile
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco123 address 200.0.0.0 255.255.255.0Configuration Branch B and C as GM
for configuration in branch office is simple we need to configure crypto map profile GDOI and pointing to KS router
crypto isakmp policy 10
authentication pre-share
crypto isakmp key cisco123 address 200.0.0.0 255.255.255.0
crypto gdoi group GET
identity number 10
server address ipv4 200.0.0.1
crypto map MAP1 10 gdoi
set group GET
crypto map MAP1Apply to interface facing to the WAN
int eth 0/0
crypto map MAP1Configuration Routing each site
for this case we need to make sure all of the router in network have reachbility or routing table for 10.0.0.0/8, we create EIGRP as a routing for this case
router eigrp 1
network 10.0.0.0
network 200.0.0.0Verification
- From HQ we can check with commands
show crypto gdoi ks members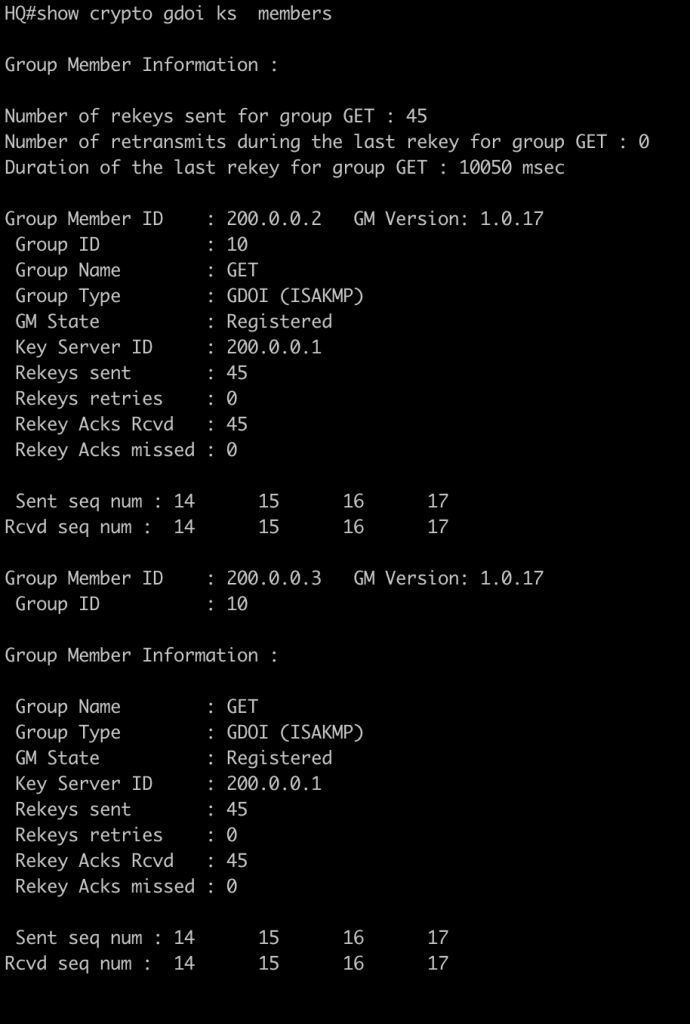
2. From Branch we can check gdoi is establish with commands
show crypto gdoi gm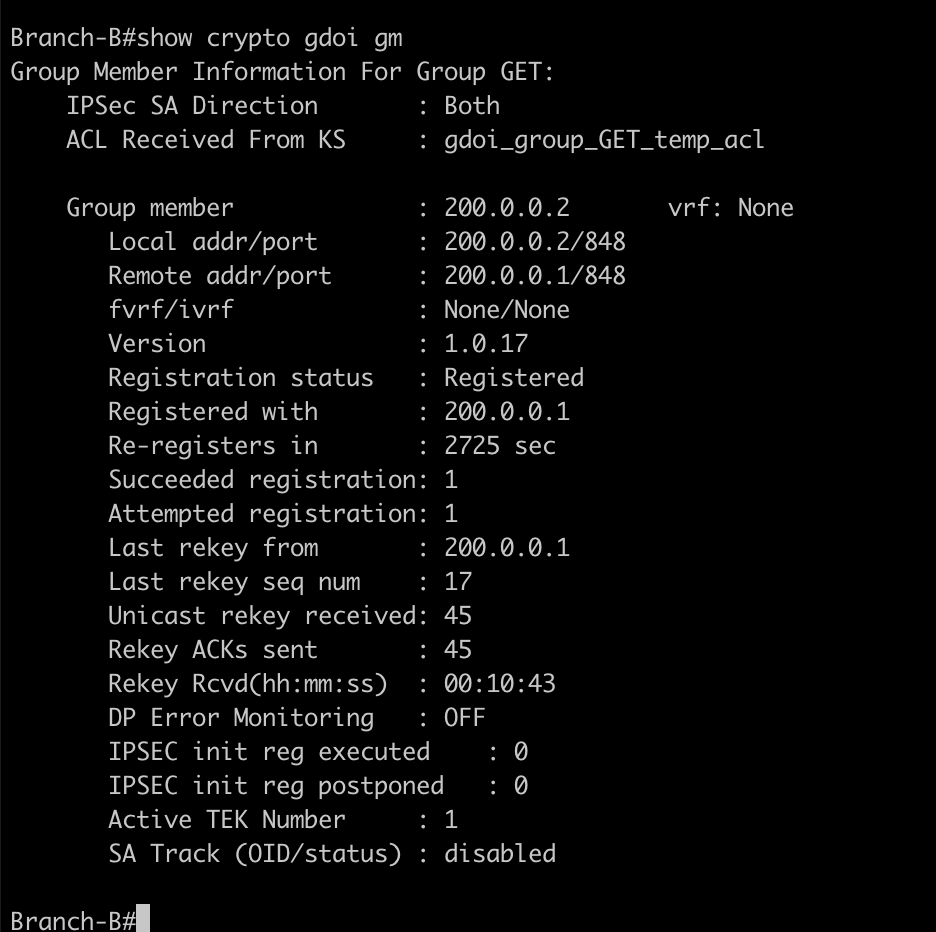
3. we can also check the acl is downloaded in gm or Branch
show crypto gdoi acl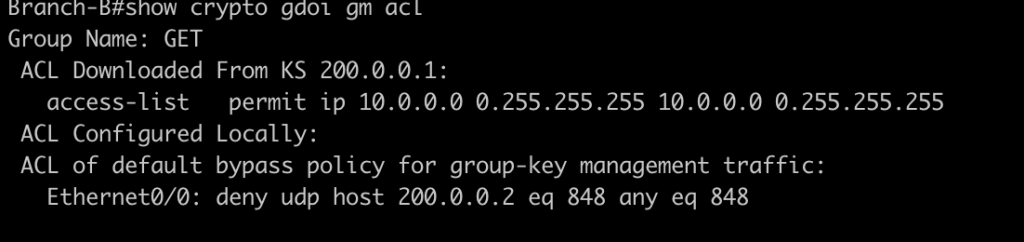
4. testing connectivity from each branch, and check if the packet is encrypted via IPsec
ping 10.20.0.1 source lo0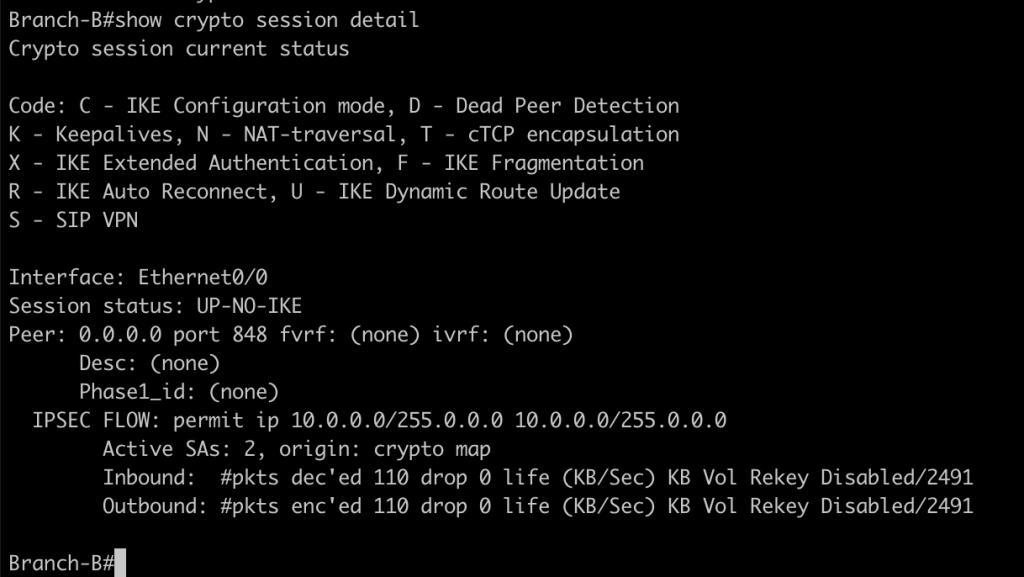
Conclusion
- with GEVPN we can easly configure IPsec VPN for each site without full mesh connectity.
- configuration in each site is simple
- with rekey we the key is periodic refresh from KS to GM
If you found this useful, subscribe to newsletter